Cryptomator.
Boxcryptor.
— more information www.boxcryptor.com/en/blog/post/cryptomator-check-cloud-encryption/
ProtonDrive is under active development, and we aim to have a public beta later this year 2020.
Cryptomator.
Boxcryptor.
— more information www.boxcryptor.com/en/blog/post/cryptomator-check-cloud-encryption/
ProtonDrive is under active development, and we aim to have a public beta later this year 2020.
Facebook is like a bad high school party — you don’t really want to be there, but feel like you have to go. – Paul Agone
X CLOUD, SECURITY AND PRIVACY FULLY ASSURED
https://privacyandsecurityoninternet.wordpress.com/2020/03/06/x-cloud-security-and-privacy-fully-assured/
— Lees op privacyandsecurityoninternet.wordpress.com/2020/03/06/x-cloud-security-and-privacy-fully-assured/
Cloud service security and privacy depends on all layers and protocols your files are transmitted by. Hence a fully privacy and security is of paramount importance.
What makes X Cloud different? In X Cloud you are really the owner of your files, they encrypt your documents and fragment them into several pieces and thanks to their use of Blockchain technology each piece of your file goes to different nodes completely encrypted and only you know the password to open them since they don’t have access to it.
Did you know even the “From:” field in an email, so the sender email address itself, can be compromised in standard email?
Regular email has no class protection.
Class 1 protection declares that the sender is the owner of the “From:” email address in the sense that the sender can receive email sent to that address, and so merely proves that an email received really did come from the “From:” address given.
Class 2 protection provides a more in-depth identity verification process, and this involves making inquiries about the would-be certificate holder.
S/MIME provides the following cryptographic security services for electronic messaging applications:
iOS offers support for S/MIME so that you can send encrypted email messages.
— more: support.apple.com/en-us/HT202345
E-mail by default is infringing your privacy. No law for privacy applies, like there is with regular (non-digital) mail.
Exchange provides an environment to support a degree of privacy on an iPhone or iPad: “In iOS 13.4 and later, when you reply or forward a message, the encryption state of your message will match the state of the incoming message rather than your system default setting.“

Authy is a free mobile / desktop app for two factor authentication, as well as security partner and SMS delivery service of many websites that want to make two-factor authentication work better for their users.
authy.com
How often do you use this app? Feel free to answer and comment.
Extra verification, many websites depend on reCAPTCHA. In 2009 this services is acquired by Google. Wikipedia states:
The current iteration of the system has been criticized for its reliance on tracking cookies and promotion of vendor lock-in with Google services; administrators are encouraged to include reCAPTCHA tracking code in all pages of their website to analyze the behavior and “risk” of users, which determines the level of friction presented when a reCAPTCHA prompt is used. Google stated in its privacy policy that user data collected in this manner is not used for personalized advertising. It was also discovered that the system favors those who have an active Google account login, and displays a higher risk towards those using anonymizing proxies and VPN services.
https://en.wikipedia.org/wiki/ReCAPTCHA
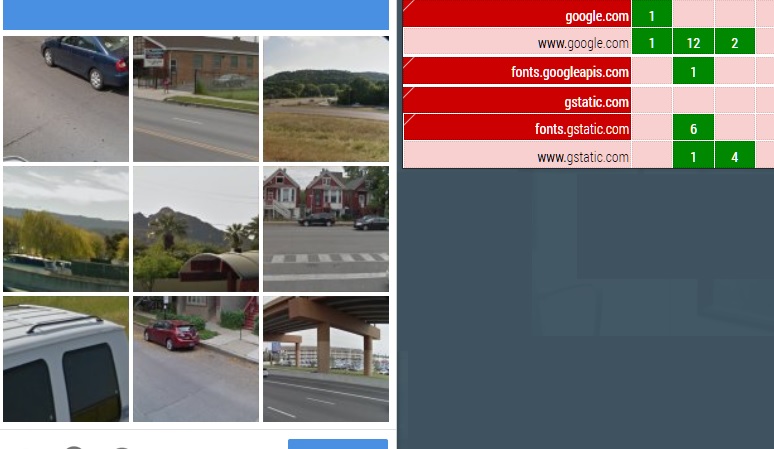
In my opinion this service should be open-source software code. Not used by tracking companies to restrict acces to a website if not used. So no gstatic.com no google.com no googleapis.com. In the above screenshot the reCAPTCHA can only be submitted if allowed to use:
2 cookies, 2 from google.com.
20 Cascading Style Sheets (or CSS), 12 from google.com, 1 from googleapis.com and 7 from gstatic.com (gstatic is also part of Google); a style sheet language used for describing the presentation of a document written in a markup language like HTML. Privacy infringement: it allowed websites to uncover a user’s browsing history and figure out what sites the user had visited. Combined with other Web technology such as JavaScript or simply loading of background images, lets Web pages determine whether a URL is in the user’s history very quickly and without any interaction from the user. This is mitigated by browsers.
6 images, an (leaky) image can reveal whether the user is visiting a specific website. None from third-party sources.
As VPN is already well known among privacy aware internet users, now a new generation VPN comes available. It is called WireGuard and it has benefits compared to mainstream OpenVPN protocol.
https://www.privateinternetaccess.com/blog/wireguide-all-about-the-wireguard-vpn-protocol/
The link above explains WireGuard. Technically explained.

The rapid penetration of Digital technologies into almost every sphere of life has revealed how fundamentally limited Privacy protections conceived …
The rapid penetration of Digital technologies into almost every sphere of life has revealed how fundamentally limited Privacy protections conceived …